Windows Notepad RCE, the RCE All Hackers Have Dreamed Of
Source: NSB Cyber
The cyber security space was surprised by what was found in Windows February 10 Patch Tuesday notes: a high-severity remote code execution (RCE) vulnerability in its Windows Notepad application. The issue is tracked as CVE-2026-20841 and carrying a CVSS v3.1 score of 8.8 to underscore a serious risk if left unpatched. The Microsoft’s advisory also highlighted that while no widespread exploitation had been observed in the wild at the time of the release, the flaw could enable attackers to execute untrusted code when users interact with malicious content.
Now, RCE in this case does not mean that an attacker can execute code remotely on the victim (point and click exploit), but that a user that interacts with a malicious file can unexpectedly execute code hosted on an attacker infrastructure.
More importantly, this vulnerability did not affect the classic legacy Notepad.exe that has shipped with Windows for decades. Instead, it impacted the modern Microsoft Store version of Notepad, which gained richer features like Markdown rendering and clickable links in recent builds. Versions of the Store-distributed Notepad prior to build 11.2510 were considered vulnerable; updating to version 11.2510 or later through the Microsoft Store mitigates the issue.
The underlying issue stemmed from a command injection weakness in the way the modern Notepad app handled certain elements of Markdown files. An attacker could craft a seemingly innocuous .md file with embedded malicious links that, once opened and clicked by a user, triggered Notepad to process unsafe protocols. This could allow execution of remote or local payloads under the context of the logged-in user potentially escalating to broad compromise if that user has elevated privileges.
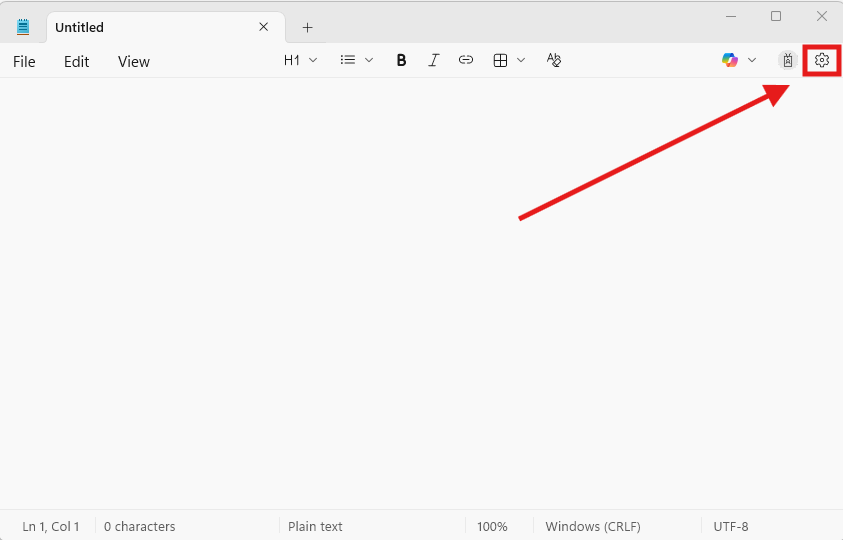
Do you know if you’re vulnerable? Here are two quick ways to find out:
Step 1: Open Notepad RCE and click on the Settings option on the top right corner.
Source: NSB Cyber
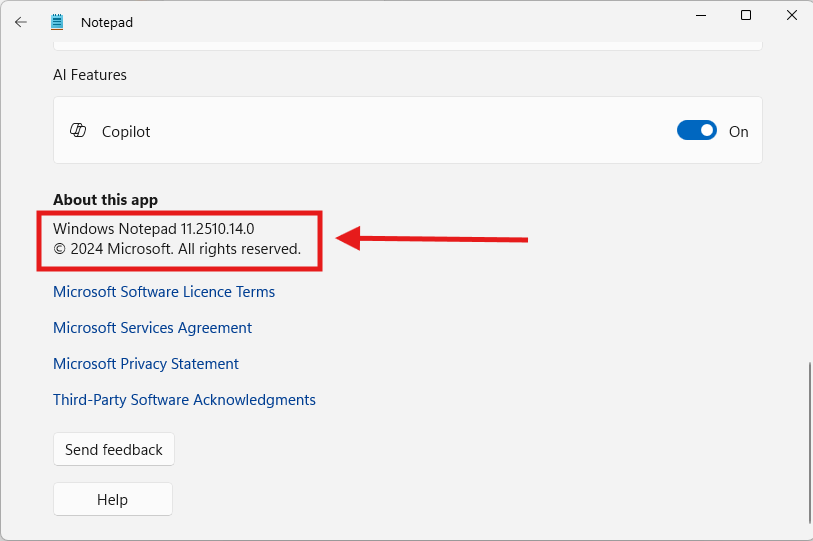
Step 2: Scroll down or resize the window until you see the version. If you see 11.2510.x then you are on the patched version.
Source: NSB Cyber
Now, for a bit of a technical analysis, CVE-2026-20841 originates in improper neutralisation of special elements in commands (classified as CWE-77: Command Injection) within the URI/protocol handling logic. The attack vector requires user interaction (opening a malicious Markdown file and clicking a link), and the Network attack vector designation reflects that the malicious link can reference remote resources.
An RCE via Notepad has been a joke/dream for hackers in the last 20 years, and we finally have it!
Lastly, the usual pointers to stay safe:
Regularly keep your Windows OS updated via the regular patching cycles like the monthly stable releases.
If you have monitoring (EDR, XDR, etc.) in place, monitor for egress traffic - not just ingress. This exploit specifically requires the victim to click on a link that loads external resources that are then executed. While the .md file can look benign, the egress traffic will show users reaching for potentially malicious resources or files.
Do not blindly trust files from unknown sources. The issue is now patched, but as a general rule, do not trust the internet and do not trust attachments in emails (unless you trust the sender).
Want to stay on top of the latest breaches and incidents, sign up to our LinkedIn Newsletter or check our Signals page every Friday!